Apr 23, 2026
MFA doesn't stop session cookie replay. Endpoint detection doesn't catch fileless malware without behavioral analysis. Here's the full post-phishing kill chain and what actually stops it.
Apr 21, 2026
Cracking NTLMv1 SSP With Rainbow Tables
Hunter Wade
Penetration Tester
Step-by-step walkthrough of cracking NTLMv1-SSP hashes with rainbow tables, including how to coerce auth, disable ESS, recover NT hashes, and remediate.
Apr 16, 2026
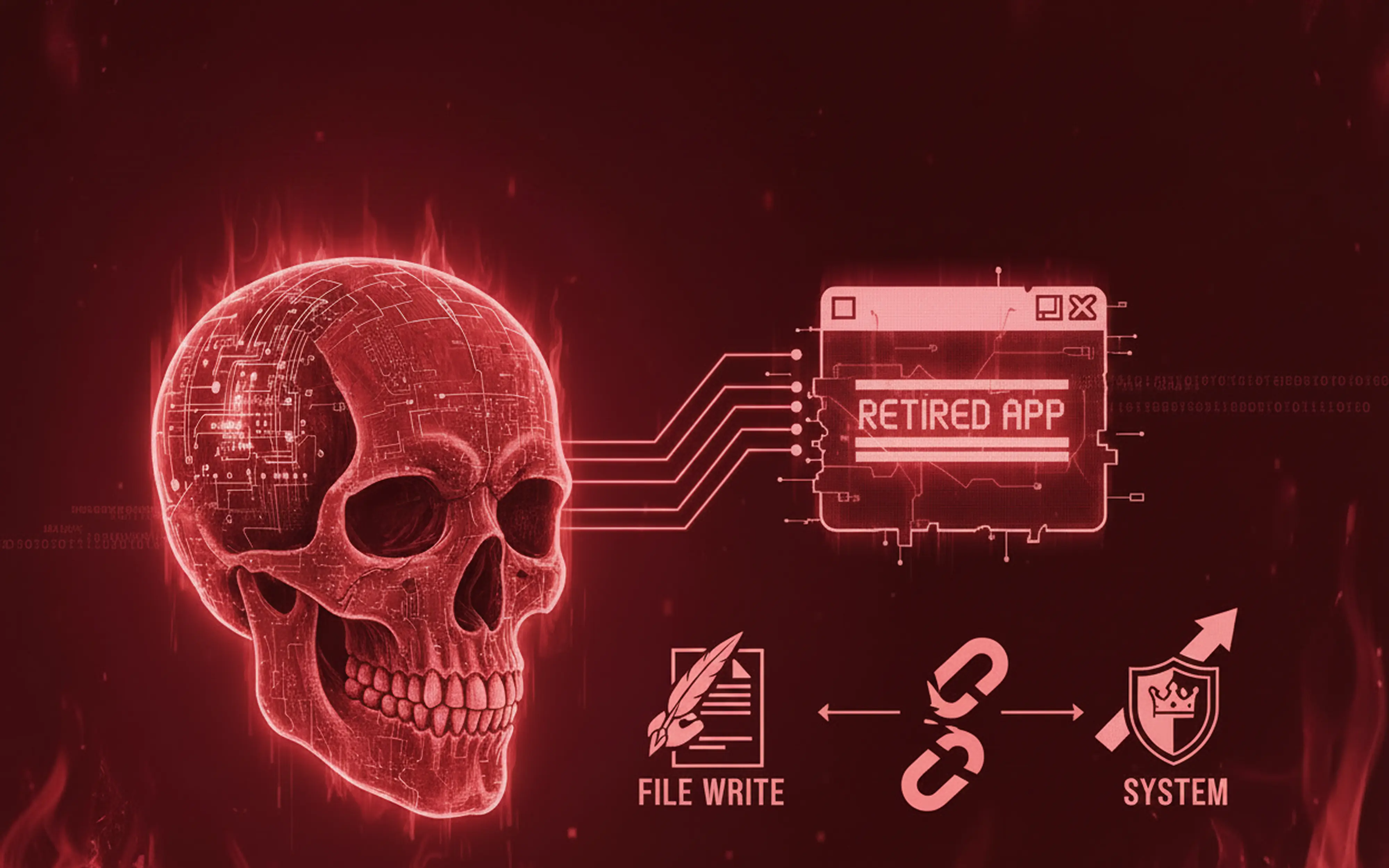
Vulnerability Hunting a Retired App Part 2 - From File Write to SYSTEM
Nick Aures
Senior Penetration Tester
Discover how an unsanitized file write endpoint in Omega Enterprise Gateway escalates to SYSTEM-level code execution and what dead code reveals about real-world security bugs.
Apr 13, 2026
Jack Willis
Software Developer
A successful prompt hack looks like your system working correctly for someone else. The mechanism that makes this possible is the same one you’re paying for.
Apr 10, 2026
That "Windows Update" Could Be Stealing Your Passwords
Topher Lyons
Solutions Engineer
Attackers are using a fake Microsoft support page to deliver password-stealing malware disguised as a Windows update and antivirus tools missed it entirely. Learn how the attack works and what your team can do to stay protected.
Apr 09, 2026
Ahead of the Breach – Andy Grant on Offensive Intuition and Letting Hackers Hunt
Andy Grant explores what happens when you remove time-boxes, checklists, and rigid scope from offensive security and trust skilled engineers to follow their intuition.