By 2025, the boardroom debate about “moving to the cloud” is largely over. It has been replaced by the far more complex engineering reality of managing the resulting sprawl.
This article focuses on the implications of Hybrid vs Multi-Cloud in 2025 for Systems Engineers.
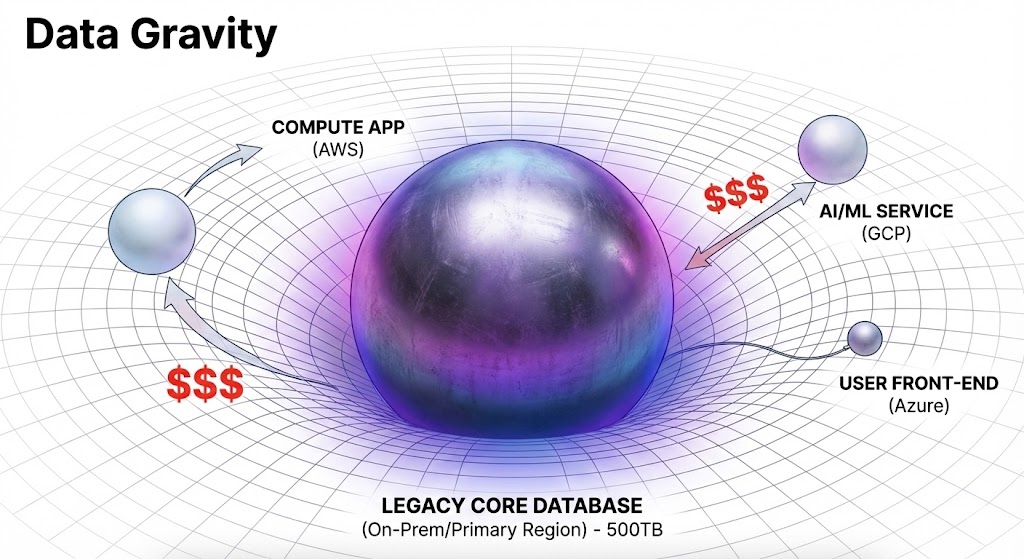
For Systems Engineers (SEs), infrastructure architects, and platform teams, the definitions of “Hybrid” and “Multi-Cloud” have shifted from marketing buzzwords to descriptions of operational burden. We are no longer chasing the fantasy of “seamlessly moving workloads with a single click.” We are dealing with the friction of networking, the crushing weight of data gravity, and the nightmare of fragmented identity planes.
This article cuts through the vendor fluff to define what Hybrid and Multi-Cloud actually look like on the ground in 2025, and the specific challenges engineers need to master to survive them.

Defining the 2025 Landscape without the Buzzwords
Let’s reset the definitions based on what we see in production environments today.
The Hybrid Reality: The Tethered Anchor
Hybrid Cloud in 2025 isn’t a temporary state on the way to “all-in.” It is a permanent architectural choice driven by physics and economics.
It means you have significant on-premises infrastructure—mainframe, massive manufacturing databases, specialized OT hardware, or regulatory-bound storage—that simply cannot move. The “cloud” portion attaches to this anchor to provide burst compute, user-facing front-ends, or disaster recovery sites.
The SE’s Reality: Your life revolves around the tether—the DirectConnect or ExpressRoute link. You are managing latency sensitivity between an app server in us-east-1 and a database in your Ohio datacenter. You aren’t “cloud-native”; you are “network-dependent.”
The Multi-Cloud Reality: Specialized Silos
The 2020 vision of Multi-Cloud was “workload mobility”—running the same VM in AWS today and Azure tomorrow to arbitrage costs. That vision largely failed due to data gravity and platform specifics.
In 2025, Multi-Cloud means “Best of Breed Silos.”
- You use Microsoft Azure because your company runs on M365 and Active Directory, making Entra ID the path of least resistance for corporate OS workloads. This often leads to adopting the Azure Landing Zone architecture for governance.
- You use AWS because your developers built their CI/CD pipelines around Lambda and S3 five years ago and refuse to re-platform.
- You use Google Cloud (GCP) because their data analytics and AI/ML stack are currently superior for your specific use case, requiring specialized modern data stores.
The SE’s Reality: You aren’t moving workloads between them. You are trying to build secure networking bridges and consistent governance policies across three radically different IAM models and API surfaces.
The 2025 Engineering Battlegrounds
If you are designing or managing these environments today, these are the three areas consuming your time.
The Egress Shock and Networking Spaghetti
In a single cloud, networking is relatively flat. In hybrid/multi-cloud, it is expensive spaghetti.
Data gravity is real. Compute is cheap and easy to move; multi-terabyte datasets are heavy and expensive to move. SEs in 2025 are constantly battling “egress shock”—the surprise bill when an application in Cloud A decides to pull a massive dataset from Cloud B or on-prem.
The Engineering Challenge:
- Designing hub-and-spoke transit network architectures that don’t hairpin traffic unnecessarily, increasing both latency and cost.
- Implementing strict egress filtering and cost alerting at the network level, preventing a misconfigured dev/test app from draining the budget over a weekend.
For the full cost breakdown of what egress shock actually looks like on an invoice — and how to architect around it — see The Lift and Shift Cost Trap: FinOps and Cloud Sticker Shock.
The “Lowest Common Denominator” Tooling Trap
To manage multiple clouds, we turn to abstraction tools like Terraform, Pulumi, or Crossplane. The promise is “write once, deploy anywhere.”
The reality is that to support AWS, Azure, and vSphere simultaneously, these tools often force you to use the lowest common denominator of features. You can’t easily leverage a brand-new, hyper-specific AWS feature if your abstraction layer hasn’t caught up or if Azure doesn’t have an equivalent.
The Engineering Challenge:
- Deciding when to use the generic abstraction layer versus when to break glass and use native CloudFormation or ARM templates to access necessary features, creating “tooling drift.”
The Fragmented Security Boundary (Crucial Deep Dive)
This is perhaps the most critical challenge. In an on-prem world, you had a perimeter firewall. In hybrid/multi-cloud, your perimeter is identity, and your attack surface is fragmented across dozens of accounts and subscriptions across multiple vendors.
An attacker’s lateral movement path now looks like this: Phish a developer’s M365 credential -> Pivot into Azure -> Use a stored service principal key to access an AWS S3 bucket -> Find a backup file containing on-prem credentials -> Deploy ransomware to the VMware environment.
Because the control planes are fragmented, detecting this movement across boundaries is incredibly difficult.
The Backup Imperative: In this fractured environment, your backup strategy is no longer just about recovering deleted files; it is your only insurance policy against total platform compromise. If your production data spans three clouds and an on-prem DC, your backup data must sit outside that blast radius.
We explored the specifics of designing an immutable, isolated recovery environment in our recent deep dive: Ransomware-Ready Backup Strategy for 2025: What Every Engineer Must Know. The principles detailed there—specifically regarding administrative air-gapping—are non-negotiable in a complex hybrid design.
If you’re building a structured understanding of cloud architecture across hybrid and multi-cloud environments, the Cloud Architecture Learning Path sequences the full stack — from landing zone design through governance, egress control, and sovereign strategy.
Conclusion: The SE’s Evolving Role
The Systems Engineer of 2025 isn’t racking servers. They are a policy architect, a network traffic controller, and a cost analyst wrapped into one.
Hybrid and Multi-Cloud are not end states; they are operating models full of friction. Success isn’t defined by how many clouds you use, but by how effectively you mask that complexity from your developers while keeping the infrastructure secure and solvent.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Last Validated: Feb 2026 | Status: Production Verified
![]()
About The Architect
R.M.
Senior Solutions Architect with 25+ years of experience in HCI, cloud strategy, and data resilience. As the lead behind Rack2Cloud, I focus on lab-verified guidance for complex enterprise transitions. View Credentials →
The Dispatch — Architecture Playbooks
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.