Security Data Pipelines, Made Easy
Monad normalizes, filters, enriches, and routes your security data — cutting SIEM costs and freeing teams to focus on security.
How Monad Works
Managed Data Pipelines
Connect any security tool in minutes. No custom parsers. No engineering toil. No BS.
In-flight Data Transforms
Kill the noise before it costs you money. Filtering can strip out up to 70% of worthless data, keeping only what actually matters to your teams.
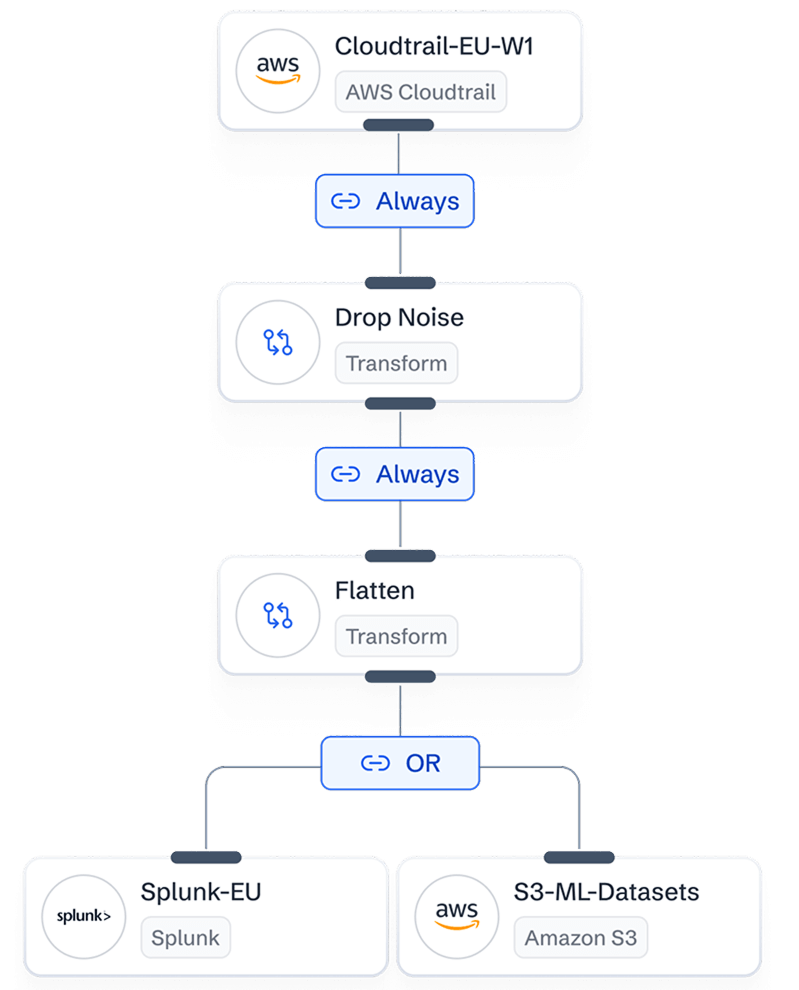
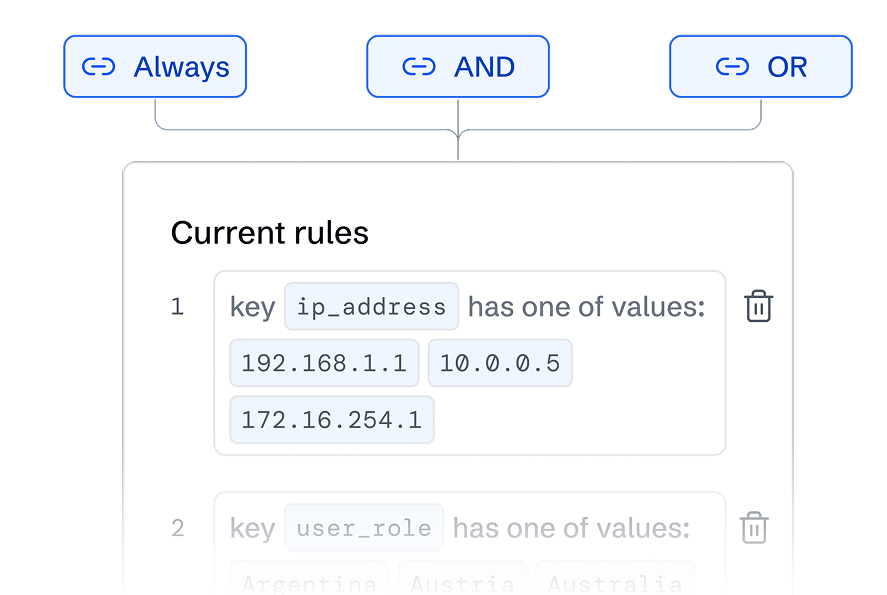
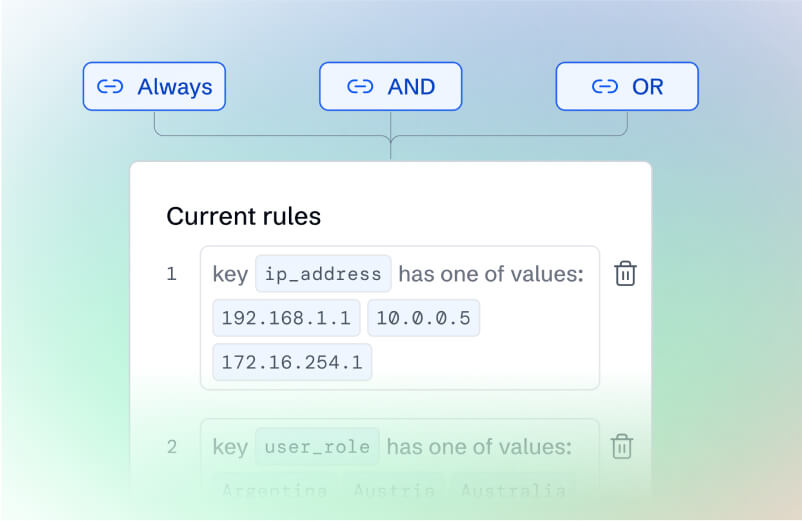
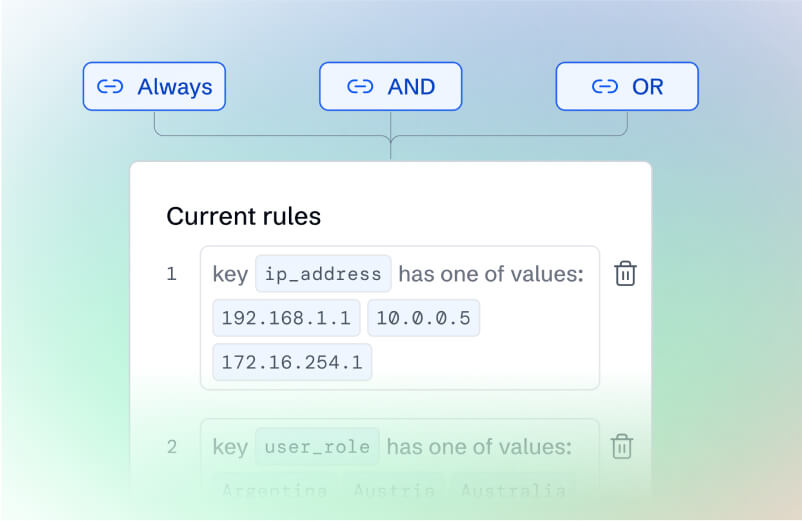
Rule-Based Data Routing
Send data where it delivers value. Intelligent routing puts high-value logs in your SIEM and archives the rest—cutting costs without losing visibility.
Deploy Your Way
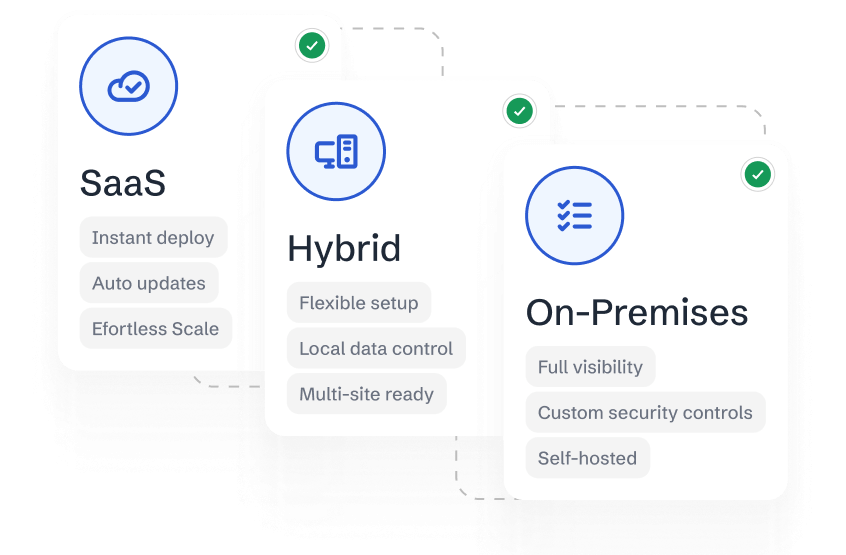
Run it wherever makes sense for your security team. SaaS for simplicity, on-prem for control, hybrid for flexibility. Same powerful platform, your choice of deployment.
Connect Everything, Effortlessly
Connect any security tool in minutes, not months. No custom parsers. No professional services. No engineering toil. Connect and go.

Splunk
Tines Events
Duo Admin Activity Logs
Wiz Findings
Semgrep Findings
CrowdStrike Vulnerabilities
CISA KEV
Azure Activity Logs
AWS CloudTrail
Okta Audit Logs
Github Audit Logs
Google Cloud Audit Logs
Why Teams Choose Monad
Cost Optimization at Every Step
Stop paying to store worthless telemetry. Smart filtering kills noise before it hits expensive storage. Less noise, lower bills, more budget for actual security tools.
Onboard in Minutes
No professional services. No implementation consultants. No 6-month deployments. Connect your first data source and see results before your coffee gets cold.
Developer-friendly ETL
Real APIs. Real SDKs. Real docs. Use Python, Go, or our REST API—whatever works for you. No proprietary languages or vendor lock-in tactics.
Scalability on Demand
Handle 10x log spikes without breaking a sweat. No capacity planning. No performance tuning. No emergency calls. Your data pipelines just work.
Get Started in Three Steps
01.
Connect Your Security Stack
Seamlessly connect your existing tools—no coding needed. Monad securely ingests your security data in minutes.

02.
Your Data, Your Schemas, Your Rules
Easily transform, normalize and enrich security data exactly how you need it.

03.
Route Data Without Limits
Route your data with precision. Monad’s rule-based routing filters and delivers data based on its contents, exactly where it’s needed.


Frequently Asked Questions
The backbone for
security telemetry.
Effortlessly transform, filter, and route your security data. Tune out the noise and surface the signal with Monad.











