Keyfob Analysis Toolkit (KAT)

This is a follow-up post from Hacking Your Car - Made Easy and an introduction to a new tool for analyzing car key fobs: the Keyfob Analysis Toolkit (KAT). I designed it using the protopirate source code and some reverse-engineering of the PANDORA firmware, but instead of being built for the Flipper Zero, it supports HackRF or any software-defined radio (SDR) that works with RTL433.
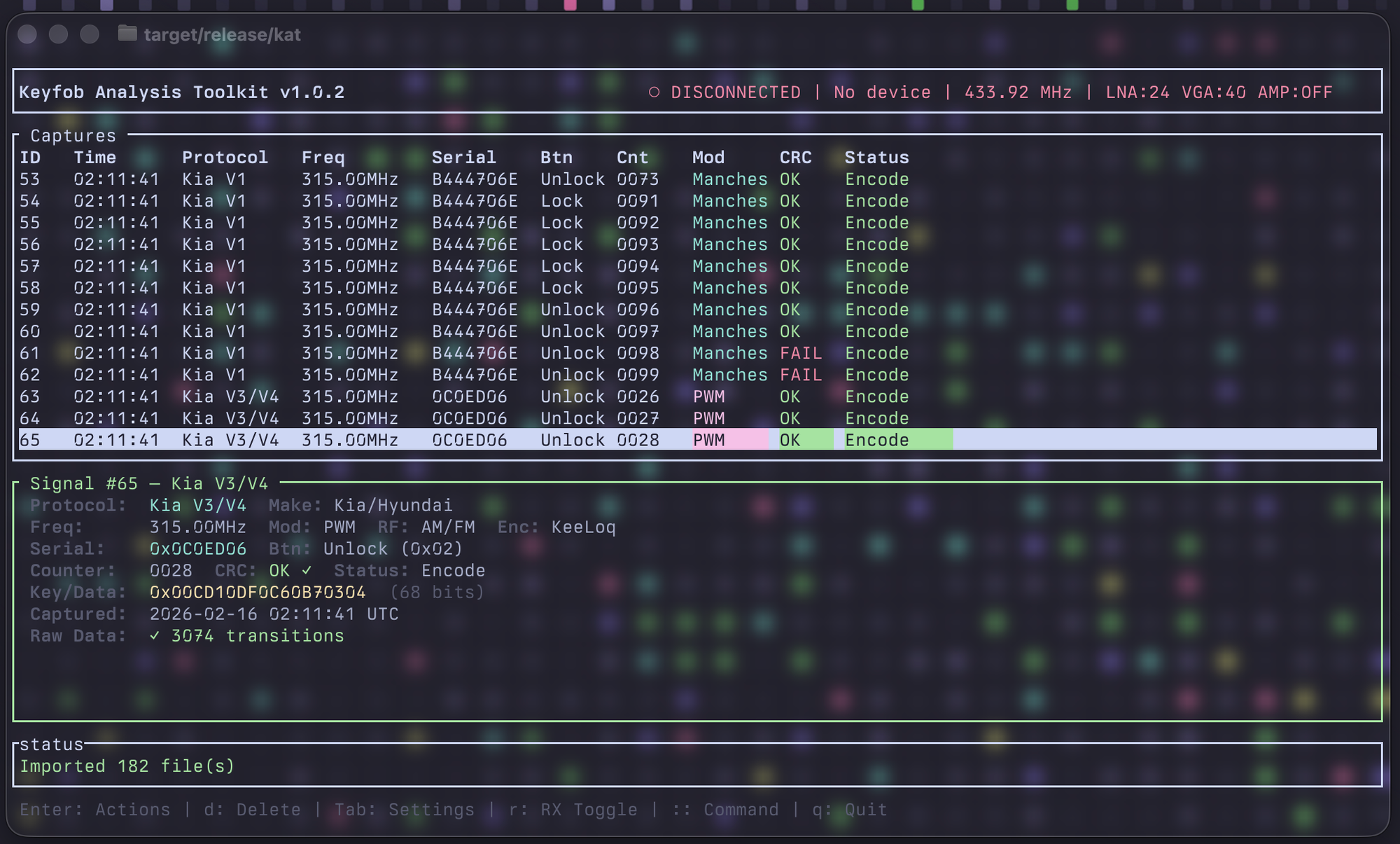
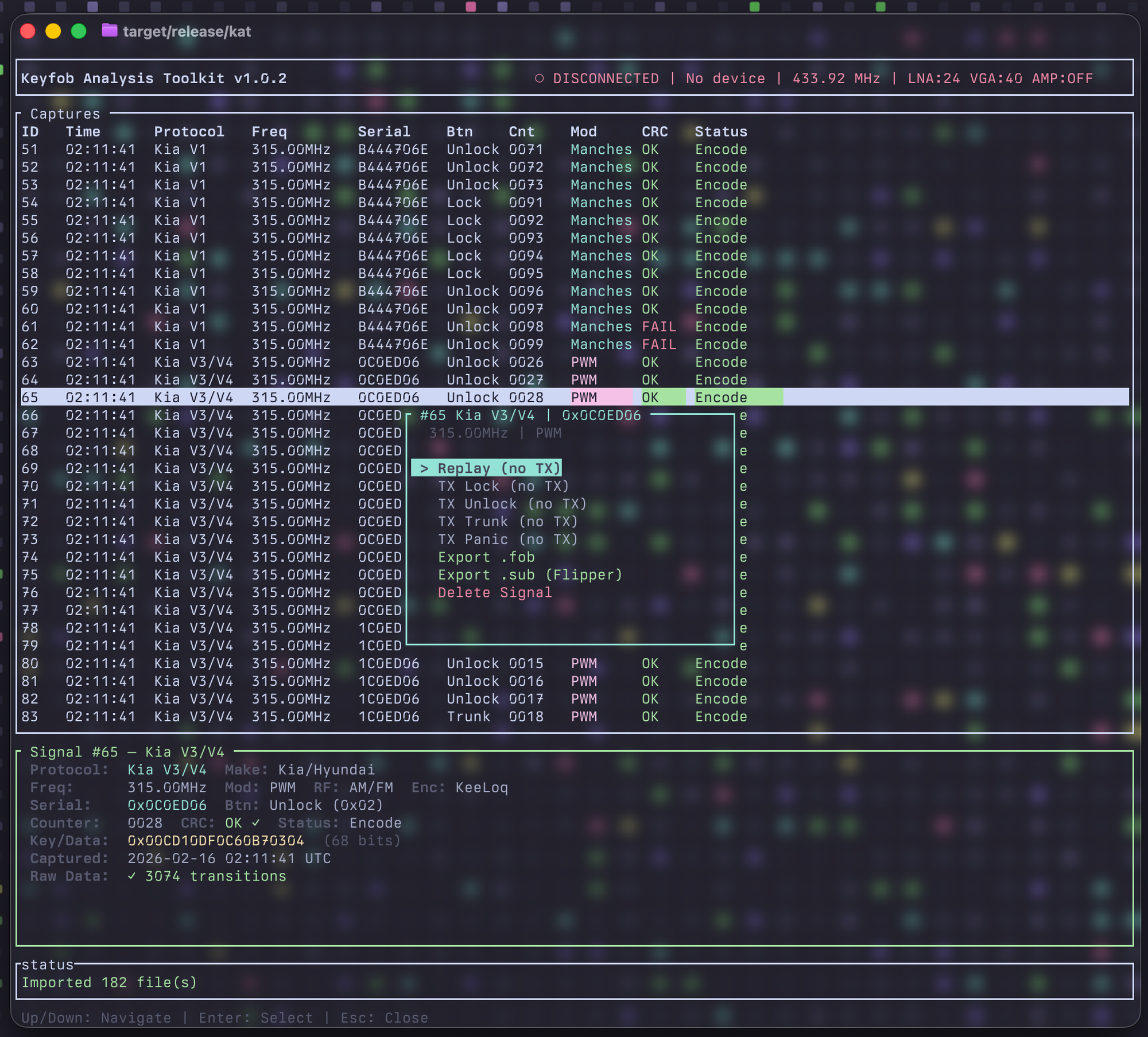
The goal of the KAT project is to develop the a toolkit to analyze signals from both automotive vehicles and gates, and to decode, retransmit, and identify potential vulnerabilities in these fobs, such as CVE-2025-6029, CVE-2022-38766, CVE-2022-27254, replay attacks, and rollback-style attacks.
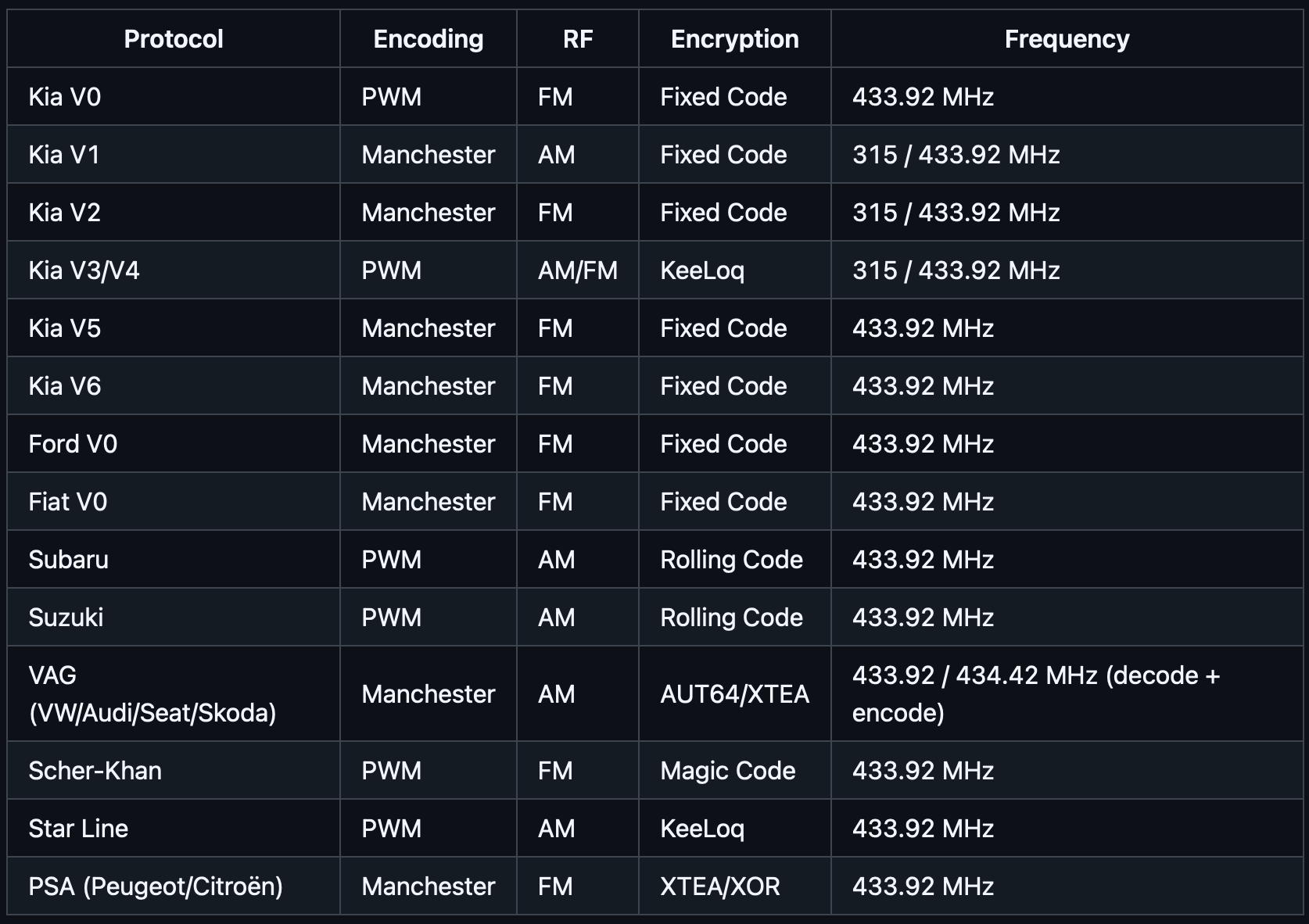
As of this writting the following decoding and encoding is available:
I hope this program can be used by security researchers to rapidly test and identify vulnerabilities across different keyfobs and the protocols that support them. There will be bugs, as this is the first release of the tool.
Find out more below
GitHub - KaraZajac/KAT: Keyfob Analysis Tool
Keyfob Analysis Tool. Contribute to KaraZajac/KAT development by creating an account on GitHub.

Security and Legal Disclaimer
Use KAT only on systems and vehicles you own or have explicit, written permission to test. Capturing, decoding, or transmitting keyfob and vehicle-access signals without authorization may be illegal in your jurisdiction (e.g. computer misuse, unauthorized access, or radio regulations). You are solely responsible for ensuring your use complies with all applicable laws. KAT is intended for security research, authorized penetration testing, education, and legitimate testing on your own equipment. The authors and contributors assume no liability for misuse or damage arising from use of this software.