Microsoft said on Wednesday that an Austria-based company named DSIRF used multiple Windows and Adobe Reader zero-days to hack organizations located in Europe and Central America.
Multiple news outlets have published articles like this one, which cited marketing materials and other evidence linking DSIRF to Subzero, a malicious toolset for “automated exfiltration of sensitive/private data” and “tailored access operations [including] identification, tracking and infiltration of threats.”
Members of the Microsoft Threat Intelligence Center, or MSTIC, said they have found Subzero malware infections spread through a variety of methods, including the exploitation of what at the time were Windows and Adobe Reader zero-days, meaning the attackers knew of the vulnerabilities before Microsoft and Adobe did. Targets of the attacks observed to date include law firms, banks, and strategic consultancies in countries such as Austria, the UK, and Panama, although those aren’t necessarily the countries in which the DSIRF customers who paid for the attack resided.
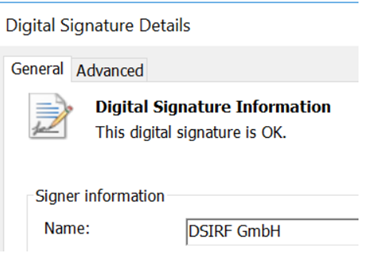
“MSTIC has found multiple links between DSIRF and the exploits and malware used in these attacks,” Microsoft researchers wrote. “These include command-and-control infrastructure used by the malware directly linking to DSIRF, a DSIRF-associated GitHub account being used in one attack, a code signing certificate issued to DSIRF being used to sign an exploit, and other open source news reports attributing Subzero to DSIRF.”
Credit: Microsoft
An email sent to DSIRF seeking comment wasn’t returned.
Wednesday’s post is the latest to take aim at the scourge of mercenary spyware sold by private companies. Israel-based NSO Group is the best-known example of a for-profit company selling pricey exploits that often compromise the devices belonging to journalists, attorneys, and activists. Another Israel-based mercenary named Candiru was profiled by Microsoft and University of Toronto’s Citizen Lab last year and was recently caught orchestrating phishing campaigns on behalf of customers that could bypass two-factor authentication.